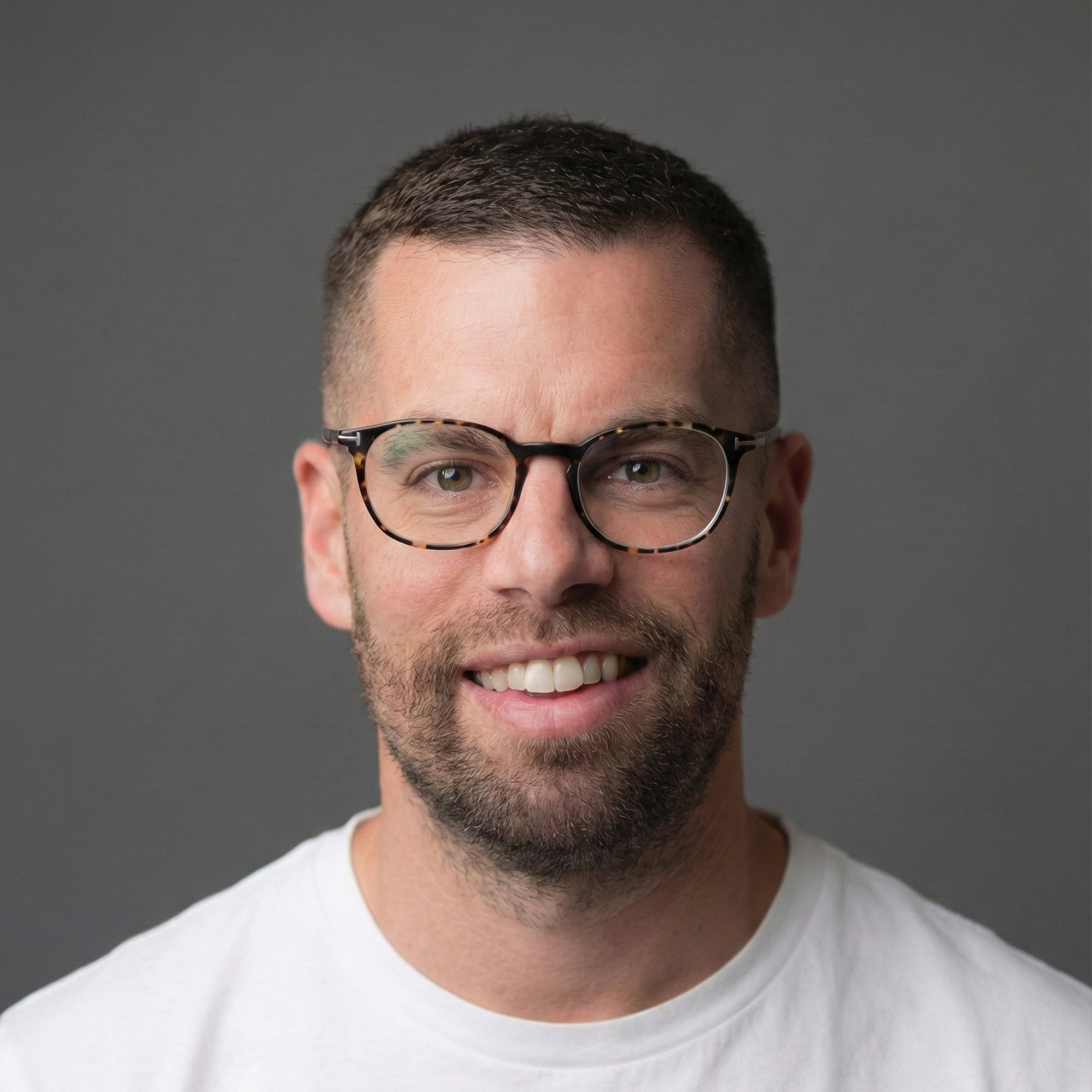
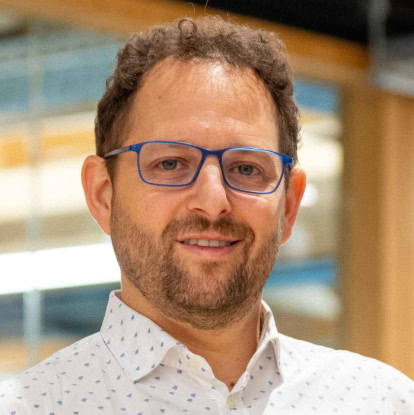
Over 18 years at the nexus of data, technology, and business transformation, I’ve shaped a career defined by innovation and leadership. As Mars’ Global Marketing Analytics Director, I leverage analytics and digital tech to fuel growth, optimize marketing, and deepen global consumer connections, guiding strategic insights to foster innovation.
Nearly 13 years at Mars underscore my expertise in leading digital transformation and implementing state-of-the-art systems. I’ve orchestrated the digital renovation of the EU Pet Nutrition Marketing division and aligned sales and marketing strategies globally. My leadership has driven significant organizational transformations, establishing agile, data-centric marketing frameworks.
I’ve directed diverse teams on complex projects, showcasing my strengths in strategic planning, IT strategy, and analytics. My roles have varied from managing business mergers, focusing on ERP integrations like SAP, to leading commercial system programs, enhancing my digitalization skills across sales to supply chain management. I’ve excelled in creating strategic roadmaps and pioneering data-driven initiatives.
Before Mars, I advanced at Netcracker from Technical Writer to Group Lead, enhancing my skills in technical communication, leadership, and managing projects globally for clients onsite in the US including Google and Intelsat.
Looking ahead, I aim to apply my extensive experience towards leadership roles in Digital Transformation and Data & Analytics, targeting positions like CIO and CDIO. My goal is to guide organizations through transformative journeys, championing innovation and inclusivity.
My career journey reflects continuous learning and adaptation, with a focus on anticipating and shaping technology and data analytics’ future. My ambition is to leverage my experience and insight to drive impactful transformations, preparing organizations to thrive in the digital age.